Share this
Cryptocurrencies, 51% and the Future of Botnets
by Reflare Research Team on May 14, 2021 7:34:00 PM
In spite of several innovative and complementary alternative decentralised financial applications being built using blockchain technology, cryptocurrencies still struggle for mainstream adoption. One of the reasons for this is a tendency for security scares resulting from apparent critical vulnerabilities in the infrastructure used by cryptocurrencies. In a single 48-hour period, such a scare hit two relatively large cryptocurrencies.
First Published 25th May 2018 | Latest Refresh 14th May 2021
A quiet life on the farm.
4 min read | Reflare Research Team
#Hodlgang
In May 2018, we saw two relatively large cryptocurrencies get hit by so-called 51% attacks leading to millions of dollars’ worth of stolen coins and heavy crashes in cryptocurrency valuation altogether. In this research brief, we will take a look at the attacks experienced by Verge and Bitcoin Gold, what 51% attacks are, and how they are likely to affect how botnets (centrally managed collections of compromised computers) are monetized in the foreseeable future.
What is a 51% attack?
The core challenge of all cryptocurrencies is how to verify a transaction without a central arbitrator. In traditional financial networks, this role is taken on by the bank or the payment processor (e.g. PayPal). The central arbitrator tracks and manages all transactions and can then subsequently make the ultimate decision on who owns what assets. If necessary, this decision may be challenged in court.
Cryptocurrencies aim to eliminate the need for a central authority. To do so, various mechanisms have been designed and adapted. However, virtually all major current cryptocurrencies rely on some form of consensus between all participants in the network. And in most of those implementations, the consensus is defined as “what 51% of miners believe”.
Since miners are performing the actual cryptographic calculations that authenticate the blocks the currency is based on and since mining power represents a strong investment, this approach is very reasonable, as long as the mining power is split between many individuals.
Centralisation Vs. Decentralisation
The original idea behind consensus-based blockchains was that if millions of people across the world were to mine for coins, it would be virtually impossible to convince all of them to agree to make bad transactions such as spending the same coin twice. After all, such transactions would be against their self-interest.
However, the large financial incentives associated with cryptocurrency mining have led to more and more mining power being controlled by fewer and fewer individuals. For example, at the time of the breach taking place, 75% of Bitcoin mining power was split between merely 6 mining pools and for a period of time in 2014, a pool named Ghash.io briefly controlled 51% of all mining power by itself.
The situation is even more dire for smaller coins with significantly less total mining power. The smaller the currency is, the less investment is required by an attacker to gain control of 51% of mining power and take over the currency. Once 51% control is achieved, transactions can be blocked, doubled or potentially redirected, giving a very large payoff for the prospective attacker.
51% and Organised Crime

With 51, the sky’s the limit.
Monetising compromised computers has always been a tricky challenge for criminals. While personal and financial information may be stolen, doing so is somewhat tedious, resulting in limited financial gain while requiring the existence of sophisticated money laundering structures.
At first, the rise of cryptocurrencies led to the widespread adoption of ransomware and mining malware. Extorting victims for money in exchange for access to their data greatly simplified monetisation strategies for attackers. Malware that directly mined cryptocurrencies for criminals is an even more streamlined process. However, abusing victim machines in 51% attacks may result in significantly greater payoffs.
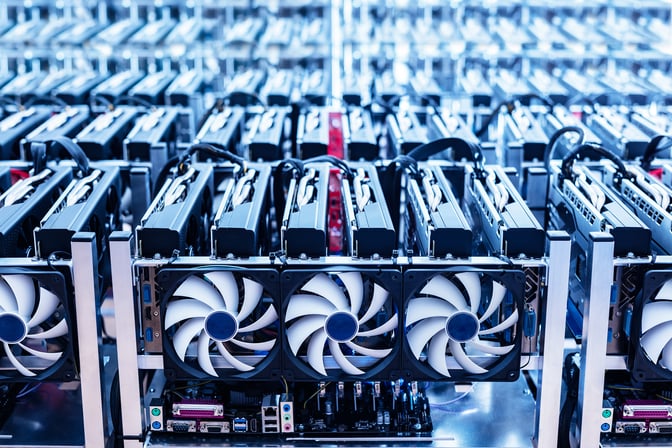
Tens of thousands of PCs infected by malware contain tens of thousands of CPUs (central processing units) and thousands of GPUs (graphic processing units). This amount of mining power is enough to overwhelm many smaller cryptocurrencies with only a few thousand miners. Once the attacker gains 51% control of the network, he or she can duplicate transactions and exchange the “forged” coins into more stable currencies before the attack is detected and the minor currency crashes.
The profits can then be invested to buy access to even more compromised machines or to directly purchase mining power on legitimate exchanges like NiceHash. Such increased mining power could then be used to attack a slightly larger cryptocurrency in the same way.
A determined, technically versed attacker might thereby leverage a moderately sized botnet into profits much larger than what he or she could currently expect.
Summary
Cryptocurrencies continue to affect how criminals monetise compromised computers. While so far, the most common adaptations are ransomware and mining malware, abusing botnets to stage 51% attacks may prove more profitable to attackers in the near future.
The more profit can be extracted from a hack, the more resources can be invested into the hack by criminals. As novel ways to monetise compromised computers - through cryptocurrencies or otherwise - are developed, we will therefore see upticks in outbreaks of malware and targeted attacks.
We advise all organisations and private individuals to remain vigilant and employ antivirus software in combination with common sense to protect themselves and their machines from attackers as the criminal marketplace continues to develop. For those businesses who have tech staff on their books, exposing developers and administrators to possess hands-on defence and attack methods will arm the wider organisation with a capability set to start addressing such a threat.
However, botnet attacks are not the only threats you must defend against. Learn how to mitigate the risks of specific hacking techniques by checking out our research briefs on other similarly related topics.
Share this
- April 2026 (1)
- March 2026 (1)
- February 2026 (1)
- January 2026 (1)
- December 2025 (1)
- November 2025 (1)
- October 2025 (1)
- September 2025 (1)
- August 2025 (1)
- July 2025 (1)
- June 2025 (1)
- May 2025 (1)
- April 2025 (1)
- March 2025 (1)
- February 2025 (1)
- January 2025 (1)
- December 2024 (1)
- November 2024 (1)
- October 2024 (1)
- September 2024 (1)
- August 2024 (1)
- July 2024 (1)
- June 2024 (1)
- April 2024 (2)
- February 2024 (1)
- January 2024 (1)
- December 2023 (1)
- November 2023 (1)
- October 2023 (1)
- September 2023 (1)
- August 2023 (1)
- July 2023 (1)
- June 2023 (2)
- May 2023 (2)
- April 2023 (3)
- March 2023 (4)
- February 2023 (3)
- January 2023 (5)
- December 2022 (1)
- November 2022 (2)
- October 2022 (1)
- September 2022 (11)
- August 2022 (5)
- July 2022 (1)
- May 2022 (3)
- April 2022 (1)
- February 2022 (4)
- January 2022 (3)
- December 2021 (2)
- November 2021 (3)
- October 2021 (2)
- September 2021 (1)
- August 2021 (1)
- June 2021 (1)
- May 2021 (14)
- February 2021 (1)
- October 2020 (1)
- September 2020 (1)
- July 2020 (1)
- June 2020 (1)
- May 2020 (1)
- April 2020 (2)
- March 2020 (1)
- February 2020 (1)
- January 2020 (3)
- December 2019 (1)
- November 2019 (2)
- October 2019 (3)
- September 2019 (5)
- August 2019 (2)
- July 2019 (3)
- June 2019 (3)
- May 2019 (2)
- April 2019 (3)
- March 2019 (2)
- February 2019 (3)
- January 2019 (1)
- December 2018 (3)
- November 2018 (5)
- October 2018 (4)
- September 2018 (3)
- August 2018 (3)
- July 2018 (4)
- June 2018 (4)
- May 2018 (2)
- April 2018 (4)
- March 2018 (5)
- February 2018 (3)
- January 2018 (3)
- December 2017 (2)
- November 2017 (4)
- October 2017 (3)
- September 2017 (5)
- August 2017 (3)
- July 2017 (3)
- June 2017 (4)
- May 2017 (4)
- April 2017 (2)
- March 2017 (4)
- February 2017 (2)
- January 2017 (1)
- December 2016 (1)
- November 2016 (4)
- October 2016 (2)
- September 2016 (4)
- August 2016 (5)
- July 2016 (3)
- June 2016 (5)
- May 2016 (3)
- April 2016 (4)
- March 2016 (5)
- February 2016 (4)


