The vulnerability allows anyone who knows it exists to remotely execute arbitrary commands on servers using default installations of Apache Struts and Java, leaving sensitive data exposed without authentication.
First Published 15th September 2017 | Latest Refresh 27th September 2017
It's only a coincidence that CEO Richard Smith retired two weeks later. Yep, only a coincidence.
3 min read | Reflare Research Team
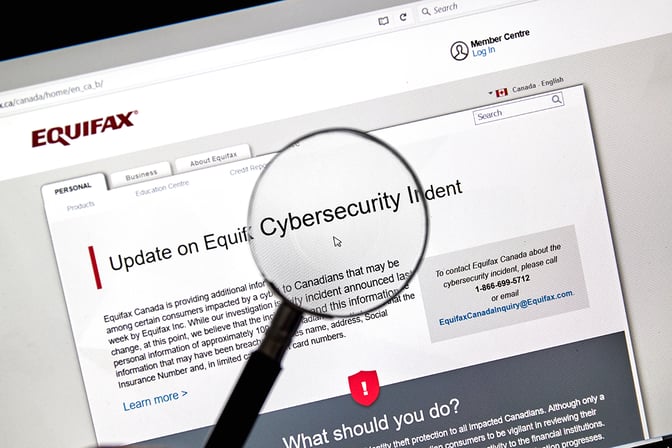
Shortly after our previous briefing covering a new vulnerability in Apache Struts and pointing out how dangerous it was, US Credit Reporting company Equifax reported a major breach of its systems. As it turns out a different vulnerability in Apache Struts was responsible for the breach. In this briefing, we will take a look at the incident and how it relates to our previous briefing.
What happened?
In a breach occurring between the middle of May 2017 and July 29th 2017, personal data belonging to 143 million US individuals and 44 million UK individuals might have been accessed by attackers. The long delay between the discovery of the breach and its disclosure has been heavily criticized by investors and security specialists as it has likely given attackers time to abuse the stolen information.
According to Equifax, the breach was partially performed by abusing a vulnerability in Apache Struts known as CVE-2017-5638. This vulnerability was discovered earlier in the year and a patch for it was released on March 7th 2017. This means that Equifax neglected to fix the known vulnerability in their systems for more than two months.
Why wasn’t the vulnerability fixed?
While we cannot determine what exactly led to the delay at Equifax, the reason for delayed fixes in corporate environments usually has two separate elements: The difficulty of the fix, and the motivation to perform the fix.
Fixing vulnerabilities in frameworks such as Struts is tricky. The framework must be upgraded and the application based on it re-compiled. In an ideal scenario, this should only take a few minutes, but corporate applications are often significantly more complex. For a company of Equifax’s size, it wouldn’t be surprising if hundreds of servers and programs would need to be upgraded for the fix to be implemented. Many of these programs in turn may face incompatibilities or other issues when compiling with the new version. In short, the fix could easily cost hundreds of man-hours.
Motivation is the second element of the puzzle. Information security is critical to Equifax’s business, but it is not an IT company. While improving, the understanding of information security among managers of non-IT companies is still poor on average. When faced with the choice of approving a costly fix or delaying it, there is thus a tendency to underestimate the risk of attack and delay the fix.
Summary
Vulnerabilities in frameworks are costly to fix and may put large enterprises at significant risk. At the same time, developing enterprise-level applications without frameworks is virtually impossible. The best defence against breaches such as the one that hit Equifax is the constant monitoring and quick fixing of discovered vulnerabilities. Adequate policy and training should be in place to ensure that management approves fixes in a timely manner.


