Crypto Currency Breaches, Continued
by Reflare Research Team on Oct 29, 2021 6:18:00 PM
Some time ago, CoinDash, an Israeli cryptocurrency startup, was using their ICO to raise $10 million. Just hours after it started, an unknown attacker compromised the website and took $7 million of it. Then, many were shocked this could happen. Today, crypto hacks are commonplace. Fir …
Electoral Interference, Restrictions and Anonymity
by Reflare Research Team on Oct 19, 2021 12:22:00 PM
The lack of international consensus on what exactly the Restrictive Internet Censorship and Freedom of Information laws should not have created a high-stakes game of political 'cat and mouse'. First Published 19th October 2016 Someone might be without their 'How to Frontside Smith Gri …
Mobile App Hype and Criminal Activity
by Reflare Research Team on Sep 13, 2021 2:48:00 PM
While Pokemon Go promised to bring in more players, hackers counted on the excitement generated by the launch to spread malware among users until the location services were fully available worldwide. First Published 13th July 2016 | Latest Refresh 13th September 2021 I choose you, vag …
The Trouble with Crowd Sourced Data
by Reflare Research Team on Aug 31, 2021 3:18:00 PM
A Mapbox GL JS v2.0.2 user maliciously renamed New York City. Within seconds of the attack, eBay, Snapchat, Foursquare, CitiBike and Zillow automatically fell in line, and NYC was gone. First Published 31st August 2018 The wisdom (and stupidity) of crowds. Baaaahstards! 4 min read | R …
Petya Ransomware Outbreak
by Reflare Research Team on Jun 30, 2021 6:11:00 PM
The Petya variant encrypts the MBR and rest of the hard disk drive, then attempts an operation similar to WannaCry. It displays a message informing victims that their files have been encrypted and that they should send $300 in bitcoin to a specific address to decrypt their files. Firs …
A Look at the Most Attacked Ports
by Reflare Research Team on May 15, 2021 7:43:00 PM
Although the number of attacks against most ports remains relatively low, it is critical to understand which ones are the most targeted. You should conduct a rigorous audit, evaluate your own exposure, and act accordingly... or else.
Government Authorities Raid DDoS Providers and Customers
by Reflare Research Team on May 14, 2021 7:40:00 PM
DDoS for hire services operate as a niche within the cybercrime ecosystem, are increasing in popularity as an efficient and effective option to carry out attacks, and are often sold with promises that they will never be detected. *Cough*
The Median Cyber-Attacker Isn't Even Remotely as Skilled as the Public Thinks
by Reflare Research Team on May 14, 2021 7:38:00 PM
Despite the almost ubiquitous adoption of advanced persistent threat (APT) and zero-day threat actor motifs into cyber security culture, it remains true that the vast majority of cyber-attackers are incapable of even executing the most basic of attacks.
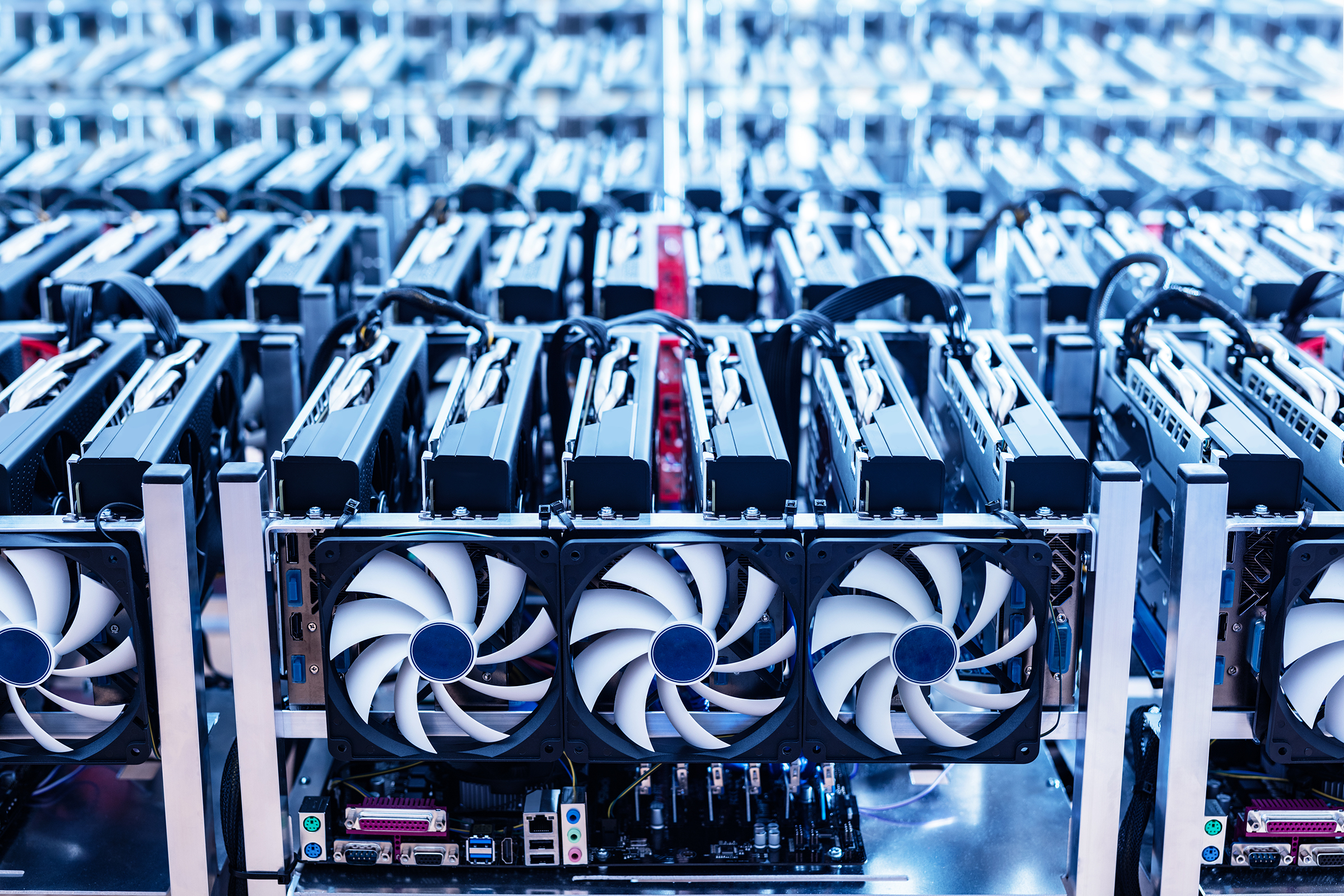
Cryptocurrencies, 51% and the Future of Botnets
by Reflare Research Team on May 14, 2021 7:34:00 PM
In spite of several innovative and complementary alternative decentralised financial applications being built using blockchain technology, cryptocurrencies still struggle for mainstream adoption. One of the reasons for this is a tendency for security scares resulting from apparent cri …
The Root of Security Bugs
by Reflare Research Team on May 14, 2021 7:30:00 PM
Even the giants can get it wrong. In November of 2017, Mac users running the then newest incarnation of Apple’s operating system — macOS High Sierra, which was released only a month before — were open to attack. The bug allowed anyone with access to the computer to log in as the “root …