Governments, Politics & Cyber Warfare
by Reflare Research Team on Jul 27, 2016 12:19:00 PM
There are three types of targets in military operations: hard, soft and targets of opportunity. In terms of cyber assignments, the same approach can be used for cyber attacks. First Published 27th July 2016 Cyber-geopolitics is gaining momentum. 4 min read | Reflare Research Team This …
The Security of ATMs
by Reflare Research Team on Jul 20, 2016 3:50:00 PM
With a large number of ATMs still running Windows XP and Windows NT4, it is becoming increasingly important to understand what the risks are in deploying these older operating systems in the modern threat landscape. First Published 20th July 2016 Insufficient funds. 4 min read | Refla …
Criminal Overlap: The Hacking Theft of Cars
by Reflare Research Team on Jul 7, 2016 3:45:00 PM
While stealing a car is nothing new, the increasing ease of doing so, combined with how long thieves are able to use stolen cars before they get flagged, makes this security threat especially worrisome. First Published 7th July 2016 "Congratulations! You've won a NEW CAAAARRRR!!!" 4 m …
Digital Polling & Public Opinion
by Reflare Research Team on Jun 29, 2016 3:40:00 PM
In the days around the Brexit vote, an online activist linked to 4chan's imageboard created multiple automated scripts allowing rapid response to petitions posted to the official UK Government petitions website. First Published 29th June 2016 Power in numbers. 4 min read | Reflare Res …
The DAO
by Reflare Research Team on Jun 22, 2016 3:37:00 PM
The DAO, a Distributed Autonomous Organisation, was created by a group of coders that set out to create the first decentralised venture capital fund. It was subsequently drained of around USD 50 million worth of Ether. First Published 22nd June 2016 'Make it Rain' with all that non-ex …
Government Sponsored Cyber Attacks
by Reflare Research Team on Jun 15, 2016 3:34:00 PM
It is no secret that global economies are becoming highly dependent on the Internet. Therefore, we should not be surprised that cyberattacks and cyberwarfare have become the tools of choice for many countries. First Published 15th June 2016 Knowledge is power. 2 min read | Reflare Res …
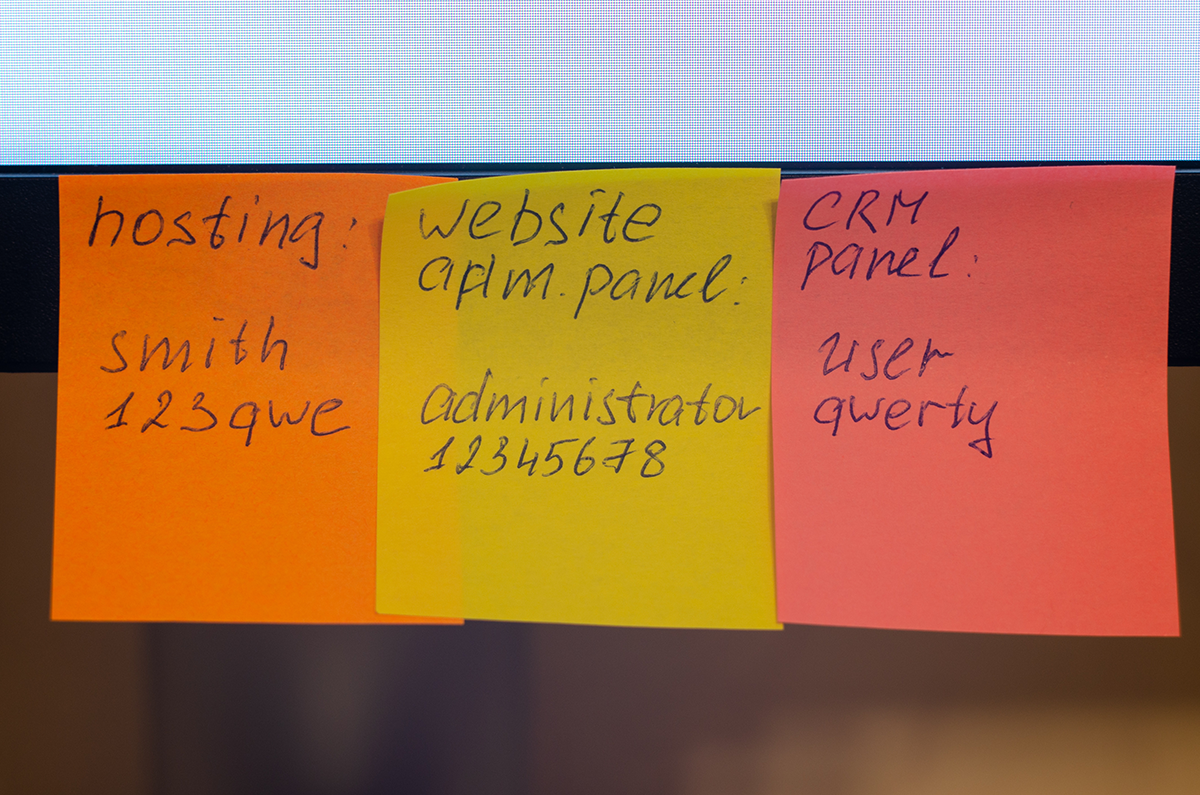
Zuckerberg & Password Strength
by Reflare Research Team on Jun 8, 2016 2:07:00 PM
Mark ended up changing his LinkedIn password to "dadada" because he couldn’t remember what it was in the first place. Not only is this a rubbish password, but also one that he used on multiple platforms; including the Facebook owned Instagram. First Published 8th June 2016 Mark is hum …
Social Media Attacks
by Reflare Research Team on Jun 1, 2016 2:04:00 PM
Social media are the preferred communication channel for many in today's world. However, it comes with a new wave of social engineering attacks that most do not understand. First Published 1st June 2016 Hacks of social media accounts are attractive due to the 'trust transfer' that alr …
Risks of Bitcoin
by Reflare Research Team on May 18, 2016 1:58:00 PM
Not only is Bitcoin a volatile market, and even if you have some knowledge of trading, most exchanges do not have adequate security in place. This has been proven in the past, and will be proven again and again in the future. First Published 18th May 2016 Choose your exchange wisely. …
Understanding the Password Black Market
by Reflare Research Team on May 11, 2016 1:55:00 PM
Some leaked password lists are so huge that they can't be ignored. However, some lists are full of junk credentials, which are meaningless to most. So why would a hacker go to the effort of posting breached passwords if they are worthless? First Published 11th May 2016 People love qua …