The Leyman's Guide to Fuzzing
by Reflare Research Team on Dec 1, 2022 7:48:00 PM
Fuzzing can (among other things) be used to expose software bugs, test browser security, and perform static program analysis. However, as the types of fuzzers continue to expand, so do their use cases.
Artificial Intelligence and Malware Detection
by Reflare Research Team on Jan 16, 2022 7:19:00 PM
The term 'artificial intelligence' is no longer a mere buzzword in the antivirus industry. But does it mean it is the holy grail for malware detection or the perfect weapon against malware developers? Not quite.
A Look at the Most Attacked Ports
by Reflare Research Team on May 15, 2021 7:43:00 PM
Although the number of attacks against most ports remains relatively low, it is critical to understand which ones are the most targeted. You should conduct a rigorous audit, evaluate your own exposure, and act accordingly... or else.
Cryptocurrencies, 51% and the Future of Botnets
by Reflare Research Team on May 14, 2021 7:34:00 PM
In spite of several innovative and complementary alternative decentralised financial applications being built using blockchain technology, cryptocurrencies still struggle for mainstream adoption. One of the reasons for this is a tendency for security scares resulting from apparent cri …
The Root of Security Bugs
by Reflare Research Team on May 14, 2021 7:30:00 PM
Even the giants can get it wrong. In November of 2017, Mac users running the then newest incarnation of Apple’s operating system — macOS High Sierra, which was released only a month before — were open to attack. The bug allowed anyone with access to the computer to log in as the “root …
New Hacking Techniques Targeting Car Keys
by Reflare Research Team on May 14, 2021 7:22:00 PM
It has been proven that hackers can communicate with the encrypted logic of a car's key fob to force it to unlock vehicles. What's more, these keys can be cloned and duplicated using off-the-shelf equipment, allowing anyone to open and drive a vehicle without the keys or validating au …
What is 00153random02009d?
by Reflare Research Team on May 12, 2021 7:16:00 PM
The usefulness of randomness is obvious. However, the probabilistic nature of computers limits their usefulness with the concept. Subsequently, you would reasonably assume that a body like the gambling industry would understand such limitations, but apparently not.
Hacking the Radio, and Other Analogue Vulnerabilities
by Reflare Research Team on May 11, 2021 7:09:00 PM
If the signal from your favourite radio station isn’t streaming smoothly to your dial, it may be malicious interference from someone who doesn’t appreciate the program you’re trying to listen to. That’s exactly what happened recently to a number of stations around the world where an i …
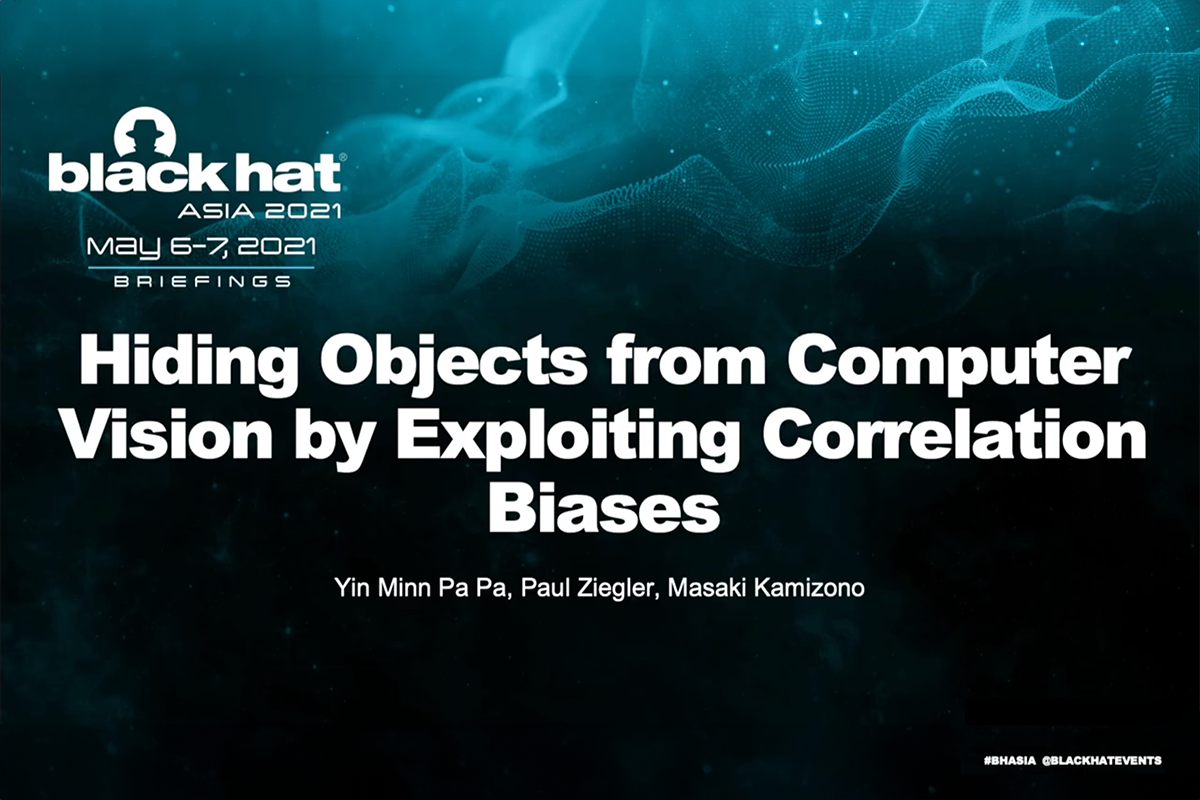
Reflare presents with Deloitte at Blackhat
by Reflare Research Team on May 9, 2021 5:05:00 PM
The results presented in this study explored the inherent correlation biases found in widely used computer vision models, which were leveraged to create images that these systems failed to interpret correctly. First Published 9th May 2021 The reversing engineer. 3 min read | 27 min vi …
Even More Evidence to Show Us the Dangers of Poorly Designed Smart Devices
by Reflare Research Team on May 7, 2021 6:09:00 PM
The increasing scale and flexibility of DDoS attacks should be a wake-up call for IoT manufacturers as such breaches become more prevalent in both consumer and industrial automation systems. But who will be able to resolve the challenge of providing security for these devices as they …